
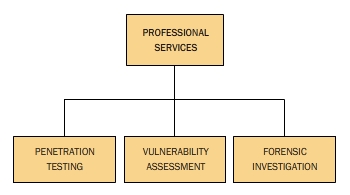
PROFESSIONAL SERVICES

The explosive growth of the Internet has brought good things like electronic commerce, collaborative computing, e-mail, information distribution, to name a few. As with most technological advances, there is also a dark side: criminal hackers. Also, no matter how extensive and layered the security architecture is constructed, an organization does not know the real potential for external intrusion until its defenses are realistically tested.
With these concerns and others, RockSecure provides in-depth Advanced Hacking and Penetration Testing services that covers testing in all modern infrastructures, operating systems and application environments. We have mastered hacking tools and their exploits. Thus, We perform the intensive assessments required to effectively identify and mitigate risks to the security of your infrastructure
WHY CONDUCT A PENETRATION TEST?
From a business perspective, penetration testing helps safeguard your organisation against failure, through:
 Preventing financial loss through fraud (hackers, extortionists and disgruntled employees) or through lost revenue due to unreliable business systems and processes. Preventing financial loss through fraud (hackers, extortionists and disgruntled employees) or through lost revenue due to unreliable business systems and processes.
 Proving due diligence and compliance to your industry regulators, customers and shareholders. Non-compliance can result in your organisation losing business, receiving heavy fines or gathering bad PR. Proving due diligence and compliance to your industry regulators, customers and shareholders. Non-compliance can result in your organisation losing business, receiving heavy fines or gathering bad PR.
 Protecting your brand by avoiding loss of consumer confidence and business reputation. Protecting your brand by avoiding loss of consumer confidence and business reputation.
From an operational perspective, penetration testing helps shape information security strategy through:
 Identifying vulnerabilities and quantifying their impact and likelihood so that they can be managed proactively; budget can be allocated and corrective measures implemented. Identifying vulnerabilities and quantifying their impact and likelihood so that they can be managed proactively; budget can be allocated and corrective measures implemented.
RockSecure will scan, test, hack and secure your systems. We perform ethical hacking and Penetration testing that evaluates a system’s security and seek answers to these basic questions:
- What can an intruder see on your target systems?
- What can an intruder do with your information?
- Does anyone at the target notice the intruder’s attempts or successes?
- What are you trying to protect?
- What are you trying to protect against?
- How much time, effort, and money are you willing to expend to obtain adequate protection?
RockSecure will evaluate the target systems’ security and report back to our Clients (the owners) with the vulnerabilities found and instructions for how to remedy them. We provide complete analysis and network security-testing services some of which (for example) are:
 Vulnerability Analysis Vulnerability Analysis
 Penetration Testing, Planning and Scheduling
Penetration Testing, Planning and Scheduling
 Firewall Penetration Testing
Firewall Penetration Testing
 Password Cracking Penetration Testing
Password Cracking Penetration Testing
 Database Penetration testing
Database Penetration testing
 Penetration Testing Report and Documentation
Penetration Testing Report and Documentation
 Internal Network Penetration Testing
Internal Network Penetration Testing
 Router Penetration Testing Router Penetration Testing
|
